Detection of wiretapping tools and devices

In a competing world everybody may, and often does have secrets. And this especially stands for the world of economy. Ferreting out and utilizing these secrets can undoubtedly confer a major advantage on the ever curious competitors.
Acquiring business secrets has of course accepted rules, everybody is free to act accordingly. Yet these game rules are not respected by everyone.
 Wiretap tools, commonly known as bugs, were once used exclusively by powerful national secret services to learn the secrets of the enemy. However, in recent decades, these tiny yet extremely efficient detection tools have become much cheaper than earlier and can be easily purchased pratically by anyone.
Wiretap tools, commonly known as bugs, were once used exclusively by powerful national secret services to learn the secrets of the enemy. However, in recent decades, these tiny yet extremely efficient detection tools have become much cheaper than earlier and can be easily purchased pratically by anyone.
On the other hand intelligence work has become more and more difficult, so today it can only be successful with appropriate technologic background and the assistance of well-trained professionals.
JUSTICE Security was the first in Hungary to apply for and be granted with the official permission to apply wiretap detection devices.
OSCOR-5000, as the core facility of our technical equipment park, represents one of the latest technologies currently available on the market.

OSCOR provides a reliable level of protection for business environment by identifying all main types of audio and video transmitter devices in the ranges of radio frequency, carrier current and infrared. With the help of this instrument our experienced professionals can identify even the most sophisticated wiretap devices within minutes.
Due to their small size bugs can be easily deployed practically anywhere without being noticed: under meeting room tables, in switches, power sockets, decoration articles, behind panelling… the list could go on endlessly.
Although invisible they still emit signals while in operation that can be detected with appropriate equipment.
Before a confidential meeting a visual check is also needed on top of the radio frequency detection. In order to perform these operations in professional manner Olympus IPLEX MX R industrial videoscope is used which- with the fibre optic inspection tools -is able to identify objects hidden even in places difficult to reach.

To detect covert devices and tools which visually cannot be directly perceived, such as microphones hidden behind wallpapers, suspended ceiling, furnishing, in electric devices, decoration article, or so-called “pin hole” hidden cameras, the available state-of-the-art ORION2.4 HX NLJD and the non-linear detectors of ORION NLJE-4000 are applied. These tools are able to detect wiretapping devices even in offline or inactive state operated with the help of SIM cards.

Our trained professionals have identified the intelligence threats associated with technologic progress: routine and experience are no longer sufficient, and sometimes even the most sophisticated RF scanner is not enough either. There was an urgent need for a new solution, a new tool in order to improve the security of the detection process.
The solution is: to assist the previously used detection tools – with a special, ultrasensitive thermal camera. The explanation is although the size of wiretap tools has by now become minimal, the heat generated by them can still reveal their presence.
Let’s take an average office, the usual accessories thereof include a power strip. As it can be seen on the left image, at first there’s nothing interesting about it.

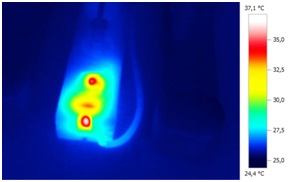
But the second photo, taken with a special thermal camera, reveals that there’s something wrong with the extension cord as in addition to the LED in the toggle switch, something else is also generating heat under the casing. This means that another tool is also operating therein. After disassembling the power strip, it becomes immediately visible that an RF operating tool has been recording and transmitting the voice from the vicinity.
The “twin pix” made with the thermal camera software gives precise information on the location of the heat emission upon jointly displaying the real image and the thermal image. The camare showing even the smallest heat difference even helps when the bug is not transmitting signs at that very moment. Thus in the course of identifying the wiretapping devices higher security factor is ensured to the clear identification of the tools.

During earlier detection (scanning) operations our professionals have found wiretapping devices in lamps, behind a painting, under a drawer, in a stapler or even in a remote control.
The camera shows even the tiniest thermal difference and can also help when the “bug” is currently not transmitting any signals. Thus, it provides a higher safety factor during the detection process of wiretapping devices for the unambiguous identification of tools.
Convince yourself that the managers’ offices are “clean” !

Before contacting us – a few good advice
Even with detection tools of this high technical level everyday precautionary measures are fundamental and indispensable. Without being aware even an internal employee can get the wiretapping appliance to a confidential meeting. Our company also undertakes to secure such kind of meetings and guarantees the security.
It is important that risk cannot be underestimated! Your business plans, carefully constructed price quotations, or patents worth of a fortune can be easily scouted with the help of really cheap tools. Do not build your corporate future on your competitors’ goodwil as the Hungarian-born former Intel CEO, Andrew Grove once said: “Only the paranoid survive”.
If you want to know how to protect yourself effectively against industrial espionage and wiretapping, do not hesitate to call our security technology advisor, György Kovács at +36 1 431 8550.
Wiretapping tool detection without authorization (just like their installation) constitutes a criminal offense!
Do not contract amateurs for this delicate task.
Preparation, planning
If your environment is under surveillance, the wiretapper may be aware of your suspicion. Detection teams rarely identify wiretapping devices, yet they often find evidence that technical tools were earlier present. If the wiretapper is aware of an impending technical inspection, the search team will probably find not even a single bug, yet wiretapping may even still go on.
The detection of wiretapping tools can fail for a variety of reasons:
- The wiretapper becomes aware of the scanning.
- The scanning is discussed via a telephone which contains a bug.
- The time and date of the scanning is pinned onto a calendar of the company.
- The wiretapper notices the arrival of the team.
- The search is conducted after the office hours, but the wiretapping device is only active during office hours.
- The scanning is conducted before the meeting, but somebody is wearing a body-mounted bug or tape recorder during the meeting.
Awareness of the client side
Scanning should not be discussed in the target building or via a telephone available therein. Only the least people possible should be made aware of an impending scanning. When planning a professional scanning, the service provider must be contacted via a phone outside the target area. It is of utmost importance to get information on the contracted service provider’s qualifications, skills and restrictions. Furthermore, the risk of an internal wiretapping can be considerably reduced if the staff knows that checks are performed on regular frequency.
Furthermore organizations should perform mini-scannings at least once a week, and before and after every important meeting. This includes physical checks of each part of the office and the easily accessible cables, and also the use of OSCOR in automatic mode for the radio frequency check of the environment.
The time of the scanning
Scanning in conference and board meeting rooms shall be as far as possible performed during working hours when it is most pobable that bugs are active. Offices and rooms accessible for all employees are recommended to be scanned in the evening hours or on weekends. Scanning shall be executed as soon as possible after the scanning team has been contacted, thus the chance is minimal that the staff becomes aware of the planned scanning.
Preparation of the environment
Taking into account that tools available on the market can be controlled remotely as well, a fictitious, but apparently plausible meeting may encourage the wiretapper to activate all devices. If the meeting is marked as very important, with the attendance of external managers as well, the wiretapper may even increase the level of surveillance. All office units (coffee machines, computers, lamps, photocopy and fax machines, etc.) shall be switched on so that each potential bug gets activated. If scanning is performed during regular office hours, the scanning staff shall also look as employees or businessmen/women. The scanning device is more efficient if it is easily portable and disguised.
Understanding the type of the threat
First it shall be identified in advance whether the threat is internal or external. Internal threats are more common yet usually less sophisticated. External threat is usually built on internal assistance to place the tools and to misappropriate corporate information. In addition the aim of the threat and the value of confidential information shall be identified. Understanding the type of threat can provide help and clues as to the type and level of sophistication of the wiretapping devices.
… you can learn more personally.